Our Services
CK Promotions offers fully managed dedicated hosting with 24/7 support. From choosing a domain name to managing your digital image online, we take care of all your website needs so you can take care of your business!

Customer Support
We offer 24/7 customer support on domain hosting. We are always just one phone call away.

WordPress Installation
Want to build your own website? Let us set-up your WordPress website for you! With easy drag & drop features you can build and maintain your own site!
Hosting Packages
We have hosting packages to suit anybody’s needs. From email only hosting to full 24/7 dedicated hosting, we have the right package for you!
Linux Shared Hosting Packages

Unlimited Traffic
No need to upgrade when your bandwidth usage exceeds the package limit.

PHP
Fast, flexible and pragmatic, PHP powers everything from your blog to the most popular websites in the world.

MySQL
With its proven performance, reliability and ease-of-use, MySQL has become one of the worlds leading database management systems.

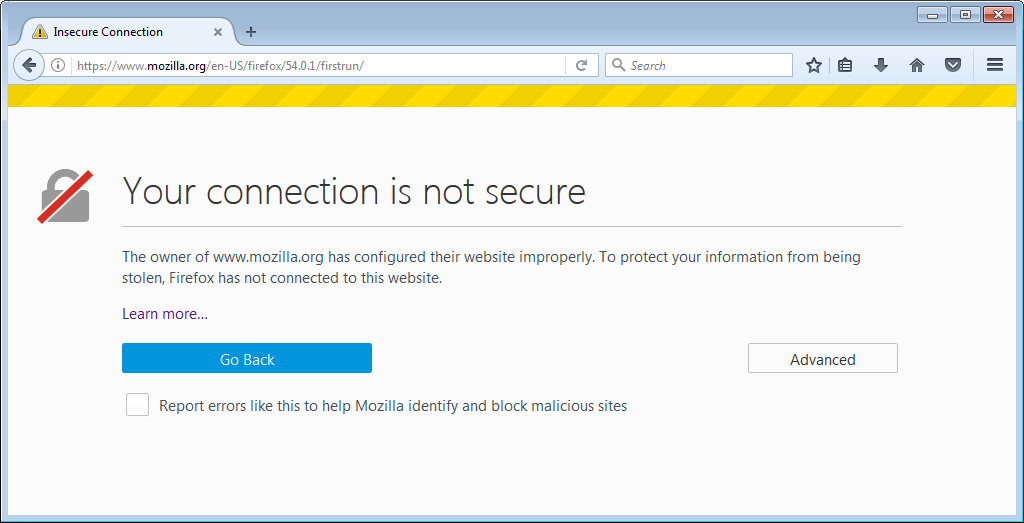
SSL Certificates
ALL our hosting packages includes a SSL certificate

The Purpose of using SSL Certificates
An SSL certificate is a type of digital certificate that provides authentication for a website and enables an encrypted connection. These certificates communicate to the client that the web service host demonstrated ownership of the domain to the certificate authority at the time of certificate issuance.1
This authentication process is much like sealing a letter in an envelope before sending it through the mail. SSL, short for Secure Sockets Layer, is commonly used on e-commerce sites and pages that require users to submit personal or credit card information.
By ensuring that all data passed between the two parties remains private and secure, SSL encryption can help prevent hackers from stealing private information such as credit card numbers, bank information, names, and addresses.
SSL Provides Trust
Web browsers give visual clues, such as a lock icon or a green bar, to make sure visitors know when their connection is secured. This means that they will trust your website more when they see these cues and will be more likely to buy from you. SSL providers will also give you a trust seal that instills more trust in your customers.
TTPS also protects against phishing attacks. A phishing email is an email sent by a criminal who tries to impersonate your website. The email usually includes a link to their own website or uses a man-in-the-middle attack to use your own domain name. Because it is very difficult for these criminals to receive a proper SSL certificate, they won’t be able to perfectly impersonate your site. This means that your users will be far less likely to fall for a phishing attack because they will be looking for the trust indicators in their browser, such as a green address bar, and they won’t see it.
SSL is required for PCI Compliance
In order to accept credit card information on your website, you must pass certain audits that show that you are complying with the Payment Card Industry (PCI) standards. One of the requirements is properly using an SSL Certificate.

🔐 Website Access & Management Policy
📌 Client access
You will have full access to update your website content—such as text, images, products, and pages—at any time.
However, access to the back-end server, hosting environment, and advanced system settings is restricted. These areas control the technical operation of the website and require specialist knowledge to manage safely. Restricting access helps protect your website from errors, security risks, and downtime.
🧠 Why Access Is Structured This Way
We follow standard web hosting and development best practices used across the industry:
- 🔒 Security Protection
Server and back-end access include sensitive areas like:
- Databases
- Email systems
- File permissions
- DNS and domain settings
- SSL certificates
Incorrect changes in these areas can:
- Break the website
- Expose data
- Allow hacking or malware
👉 Restricting access significantly reduces these risks.
- ⚙️ Technical Complexity
The back-end includes:
- cPanel / WHM configuration
- Server resource management
- PHP / software versions
- Backup systems
- Firewall and security layers
These require technical expertise and experience to manage correctly.
- 🧯 Preventing Accidental Damage
Even small changes can cause major issues:
- Deleting a file can take the entire site offline
- Changing DNS can break email
- Database edits can corrupt the website
👉 Limiting access protects your business from costly downtime.
- 🛡️ Stability & Uptime
We manage:
- Performance optimization
- Security updates
- Monitoring
- Backup and recovery systems
👉 Keeping this controlled ensures your site stays fast, stable, and online.
- 📊 Clear Responsibility & Support
When technical access is controlled:
- Issues can be diagnosed quickly
- Responsibility is clear
- Support is faster and more reliable
👤 What You Do Have Access To
You can update anytime:
- Website pages
- Text and images
- Products (if e-commerce)
- Blog posts
- Forms and content sections
👉 You stay in full control of your business content.
🔧 What Is Managed For You
We handle:
- Hosting & server management
- Security and firewall protection
- Backups and recovery
- Software updates
- Database management
- DNS and email configuration
👉 This ensures your website runs safely and professionally.
⚖️ Industry Standard Practice
This approach follows the “least privilege” principle, meaning:
Each user only has access to what they need—nothing more.
This is the same model used by:
- Hosting providers
- SaaS platforms (Shopify, Wix, etc.)
- Enterprise IT systems